---
title: Elastic Endpoint exceptions
description: Create and manage Elastic Endpoint exceptions to prevent Elastic Endpoint from generating false positive alerts for specific conditions on your hosts.
url: https://docs-v3-preview.elastic.dev/elastic/docs-content/pull/6201/solutions/security/manage-elastic-defend/elastic-endpoint-exceptions
products:
- Elastic Cloud Serverless
- Elastic Security
applies_to:
- Serverless Security projects: Generally available
- Elastic Stack: Generally available since 9.4
---
# Elastic Endpoint exceptions
In Elastic Stack 9.0–9.3, Elastic Endpoint exceptions are managed through detection rules. For more information, refer to [Add Elastic Endpoint exceptions](/elastic/docs-content/pull/6201/solutions/security/detect-and-alert/add-manage-exceptions#endpoint-rule-exceptions).
Elastic Endpoint exceptions prevent Elastic Endpoint from generating alerts for specific conditions on your hosts. Unlike [detection rule exceptions](https://docs-v3-preview.elastic.dev/elastic/docs-content/pull/6201/solutions/security/detect-and-alert/add-manage-exceptions), Elastic Endpoint exceptions are enforced directly on the endpoint — Elastic Endpoint checks for exceptions before most other processing, which means matching processes are not monitored further. This can also improve performance.
To ensure you're using the right feature for your use case, review [Optimize Elastic Defend](https://docs-v3-preview.elastic.dev/elastic/docs-content/pull/6201/solutions/security/manage-elastic-defend/optimize-elastic-defend) to understand the differences between Elastic Endpoint exceptions and other endpoint artifacts.
You must have the **Endpoint Exceptions** [privilege](https://docs-v3-preview.elastic.dev/elastic/docs-content/pull/6201/solutions/security/configure-elastic-defend/elastic-defend-feature-privileges) or the appropriate user role to access this feature.
By default, Elastic Endpoint exceptions apply globally across all hosts running Elastic Defend. If you opt in to per-policy behavior, you can also assign exceptions to specific Elastic Defend integration policies, so the exception applies only to hosts assigned to that policy.
Elastic Endpoint exceptions are space-aware: when you create a per-policy exception, it is associated with the space you're working in. For more information on how spaces interact with endpoint artifacts, refer to [Spaces and Elastic Defend FAQ](https://docs-v3-preview.elastic.dev/elastic/docs-content/pull/6201/solutions/security/get-started/spaces-defend-faq).
## Opt in to per-policy Elastic Endpoint exceptions
For deployments upgraded from an earlier version, per-policy assignment for Elastic Endpoint exceptions requires opting in. New deployments are automatically opted in to per-policy Elastic Endpoint exceptions with no action required.
If you're upgrading from an earlier version, a callout appears on the **Artifacts** page prompting you to opt in. You must have the **superuser** role in Elastic Stack, or the **admin** role in Serverless, to perform the opt-in.
Opting in is permanent and cannot be reversed. After opting in:
- Elastic Endpoint exceptions support per-policy assignment and are no longer evaluated by detection rules during rule execution.
- Elastic Endpoint exceptions can no longer be added to detection rules.
To opt in to per-policy Elastic Endpoint exceptions on an upgraded deployment:
1. Find **Artifacts** in the navigation menu, then select the **Endpoint exceptions** tab.
2. In the callout that appears, click **Update details**.
3. Review the information in the confirmation dialog, then confirm.
## Add an Elastic Endpoint exception
You can add Elastic Endpoint exceptions from the following places:
- **Artifacts page**: Find **Artifacts** in the navigation menu, select the **Endpoint exceptions** tab, then click **Add endpoint exception**.
- **Alerts table**: Find **Alerts** in the navigation menu, go to an Elastic Endpoint alert, click the **More actions** menu (`boxes_vertical`), and select **Add Endpoint exception**.
- **Policy details page**: Find **Policies** in the navigation menu, select an integration policy, then go to the **Endpoint exceptions** tab. If no exceptions are assigned yet, click **Add endpoint exception** to create a new one.
Elastic Endpoint exceptions affect all Elastic Endpoint alerts on matching hosts. Be careful not to unintentionally suppress useful alerts.
The **Add Endpoint Exception** flyout opens.
1. Fill in the **Details** section:
1. `Name`: Enter a name for the Elastic Endpoint exception.
2. (Optional) `Description`: Enter a description.
2. In the **Conditions** section, add conditions that define when the exception applies. When the exception's conditions match, Elastic Endpoint does not generate an alert for that event.
1. `Select operating system`: Select the appropriate operating system.
2. `Field`: Select a field to identify the event being filtered.
3. `Operator`: Select an operator to define the condition:
- `is`
- `is one of`
- `matches` | `does not match`: Allows you to use wildcards in `Value`, such as `C:\path\*\app.exe`. Available wildcards are `?` (match one character) and `*` (match zero or more characters).
4. `Value`: Enter the value associated with the `Field`. To enter multiple values (when using `is one of` or `is not one of`), enter each value, then press **Return**.
Unlike detection rule exceptions, Elastic Endpoint exceptions do not require escaping special characters. Enter file paths and values exactly as they appear on the host (for example, `C:\Windows\explorer.exe`, not `C:\\Windows\\explorer.exe`). Refer to [Exception types and value syntax](https://docs-v3-preview.elastic.dev/elastic/docs-content/pull/6201/solutions/security/manage-elastic-defend/exception-types-and-syntax) for syntax details and examples.
To define multiple conditions, click **AND** or **OR** and configure a new condition. You can also add [nested conditions](#nested-conditions).
3. Select an option in the **Assignment** section to assign the exception to a specific integration policy:
- `Global`: Apply the exception to all Elastic Defend integration policies.
- `Per Policy`: Apply the exception to one or more specific Elastic Defend integration policies. Select each policy where you want the exception to apply.
You can also select `Per Policy` without immediately assigning a policy. This lets you create and review exception configurations before putting them into action with a policy.
4. (Optional) Add a comment to provide more context about the exception.
5. Click **Add endpoint exception**.
It might take longer for exceptions to be applied to hosts within larger deployments.
## Nested conditions
Some Elastic Endpoint fields require nested conditions to ensure the exception functions correctly. For details on which fields require nested conditions and an example, refer to [Nested conditions](/elastic/docs-content/pull/6201/solutions/security/detect-and-alert/add-manage-exceptions#ex-nested-conditions).
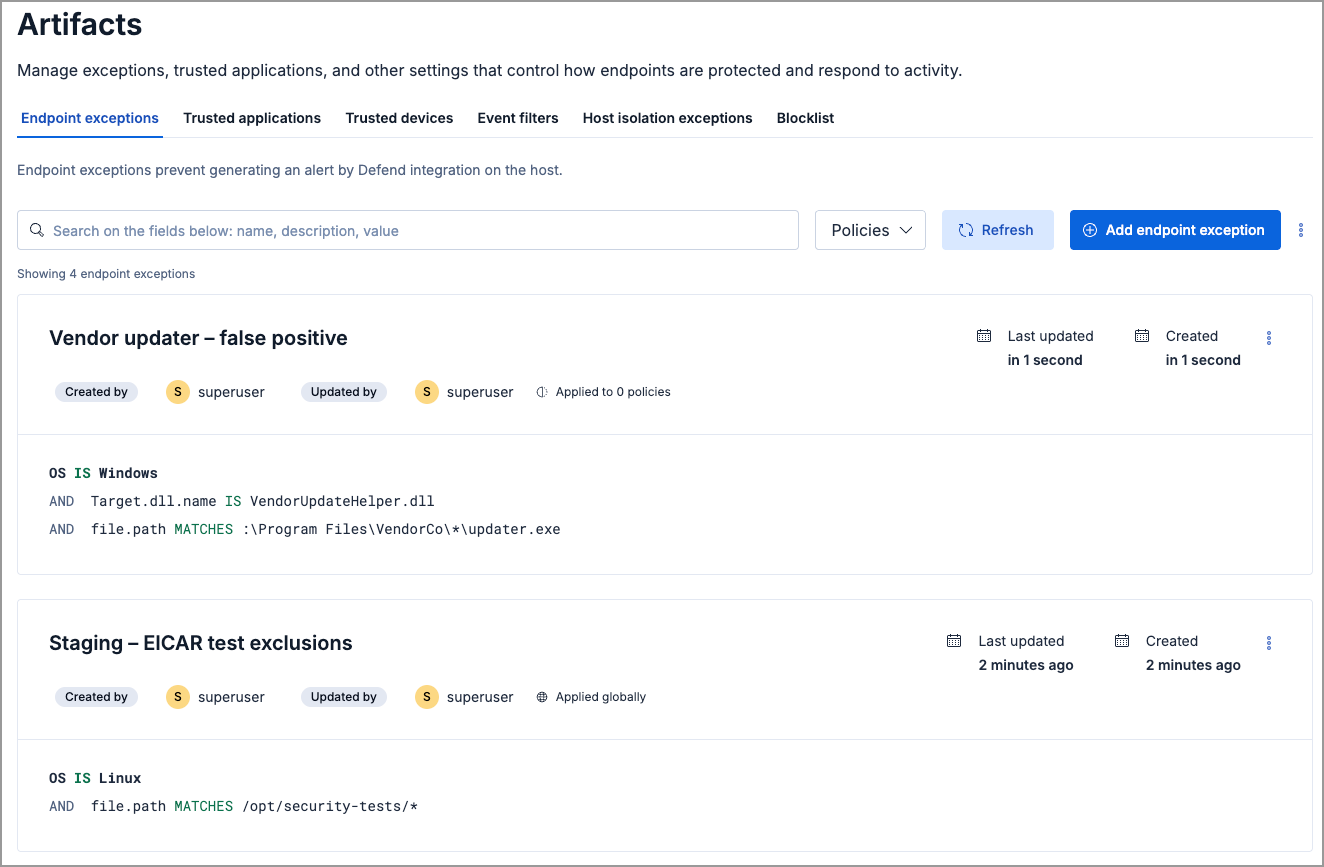
## View and manage Elastic Endpoint exceptions
The **Endpoint exceptions** tab on the **Artifacts** page displays all Elastic Endpoint exceptions added to the Elastic Security app. To refine the list, use the search bar to search by name, description, or field value. You can also use the **Policies** filter to narrow the list by policy assignment:
- Select one or more policies to show only exceptions assigned to those policies.
- Under **Additional filters**, select **Global entries** to show exceptions assigned globally, or **Unassigned entries** to show exceptions not assigned to any policy.
You can import and export Elastic Endpoint exceptions as NDJSON files using the actions menu (`boxes_vertical`) on the **Endpoint exceptions** tab.
When you import an NDJSON file, the imported exceptions are appended to your existing exceptions — existing entries are not removed or overwritten.
In versions prior to 9.4, importing offered the option to remove all existing exceptions and replace them with the imported ones. Starting in 9.4, import always appends — existing exceptions are never removed. If you're upgrading from an earlier version, this applies whether or not you have opted in to per-policy exceptions.
### Edit an Elastic Endpoint exception
To edit an Elastic Endpoint exception:
1. Click the actions menu (`boxes_vertical`) on the exception you want to edit, then select **Edit endpoint exception**.
2. Modify details as needed.
3. Click **Save**.
### Delete an Elastic Endpoint exception
To delete an Elastic Endpoint exception:
1. Click the actions menu (`boxes_vertical`) on the exception you want to delete, then select **Delete endpoint exception**.
2. On the confirmation dialog, click **Delete**. This removes the exception from all Elastic Defend integration policies.