Capture Elastic Agent diagnostics
Elastic's diagnostic tools capture point-in-time snapshots of Fleet and Elastic Agent related statistics and logs. They work against all product versions.
Their information can be used to troubleshoot problems with your setup. You can generate diagnostic information using this tool before escalating to us to minimize turnaround time.
For Fleet-managed Elastic Agent, related settings and states can by surfaced by:
- Kibana from the Kibana Fleet APIs
- Elastic Agent and Fleet from their command reference
Standalone Elastic Agents are not associated to Kibana nor Fleet, but their diagnostics are still accessible from the CLI.
To pull data from the respective applicable locations, refer to:
- Capture Kibana diagnostics
- Collect Elastic Agent diagnostics
-
Note
To pull Elastic Agent diagnostics for the managed Fleet Server on your hosted deployment, you have to use the Fleet UI. The Fleet Server agent is associated with a managed agent policy named "Elastic Cloud agent policy".
You need to determine which diagnostic types are needed to investigate your specific issue. This table shows common troubleshooting situations and which diagnostics are commonly associated:
| Situation | Kibana | Elastic Agent | Fleet |
|---|---|---|---|
| Kibana reports there's no Fleet Server | Yes | No | Yes |
| Elastic Agent is unable to connect to Fleet | No | Yes | Yes |
| Elastic Agent component or integration errors | No | Yes | No |
| Elastic Agent update issues or desynced status | Yes | Yes | No |
When in doubt, start with the Kibana and Elastic Agent diagnostics.
Some Elastic Agent configuration issues only appear in the agent's start-up debug logs. This is more common for cloud-connecting Elastic integrations which maintain checkpoints. This can cause later logs to only document that the subprocess has stopped or that it has not changed state after an earlier error. In these situations, follow these steps:
- Enable
debuglogging. - Restart Elastic Agent.
- Wait 10 minutes for the changes to sync from the Fleet Server to the Elastic Agent and for the Elastic Agent to restart.
- Pull the Elastic Agent diagnostics using your preferred method.
- Disable
debuglogging.
Elastic Agent comes bundled with a diagnostics command which generates a zip archive containing troubleshooting diagnostic information. This export is intended only for debugging purposes and its structure can change between releases.
The Fleet UI provides the ability to remotely generate and gather an Elastic Agent's diagnostics bundle if it is online in a Healthy or Unhealthy status. For Elastic Agents in other statuses, you must use the CLI to grab their diagnostic.
Diagnostics and logs mainly emit product metadata and settings, but they might expose sensitive data which needs to be redacted before being shared outside of your organization. For more details, refer to Sanitize.
The diagnostics are sent to Fleet Server which in turn sends it to Elasticsearch. Therefore, this works even with Elastic Agents that are not using the Elasticsearch output. To download the diagnostics bundle for local viewing:
In Fleet, open the Agents tab.
In the Host column, click the agent’s name.
Select the Diagnostics tab and click the Request diagnostics .zip button.
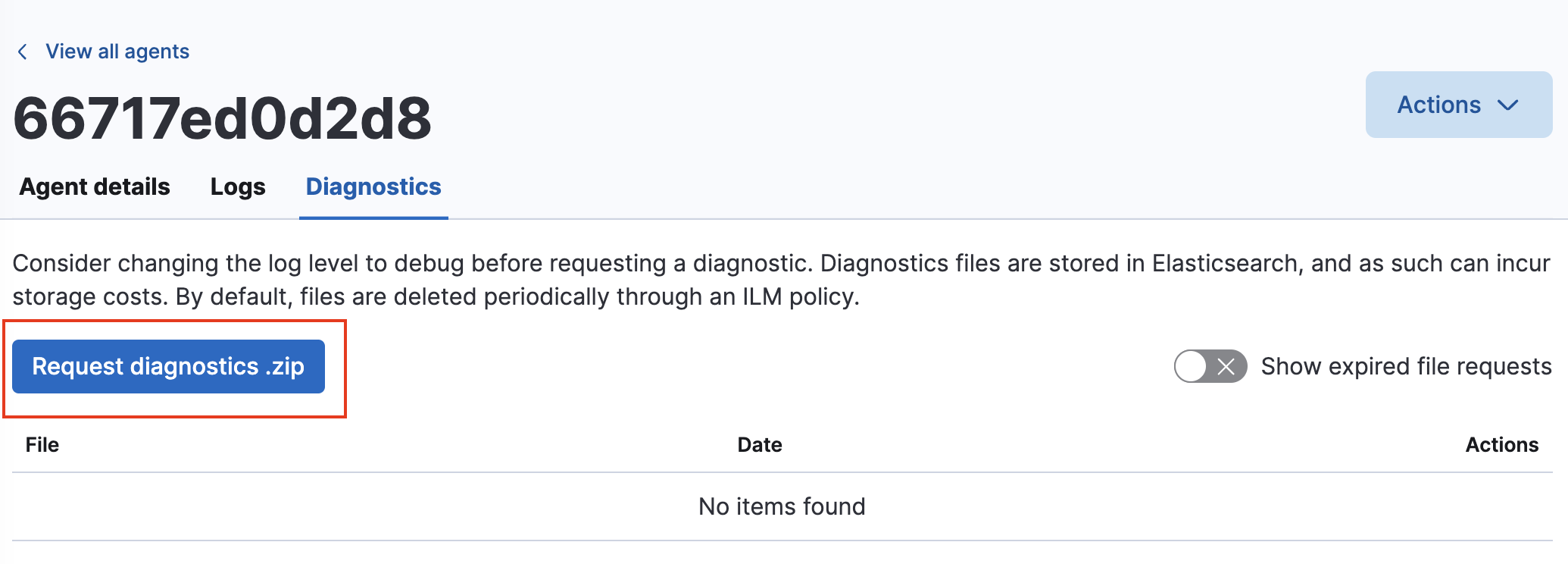
In the Request diagnostics pop-up, select Collect additional CPU metrics if you’d like detailed CPU data.
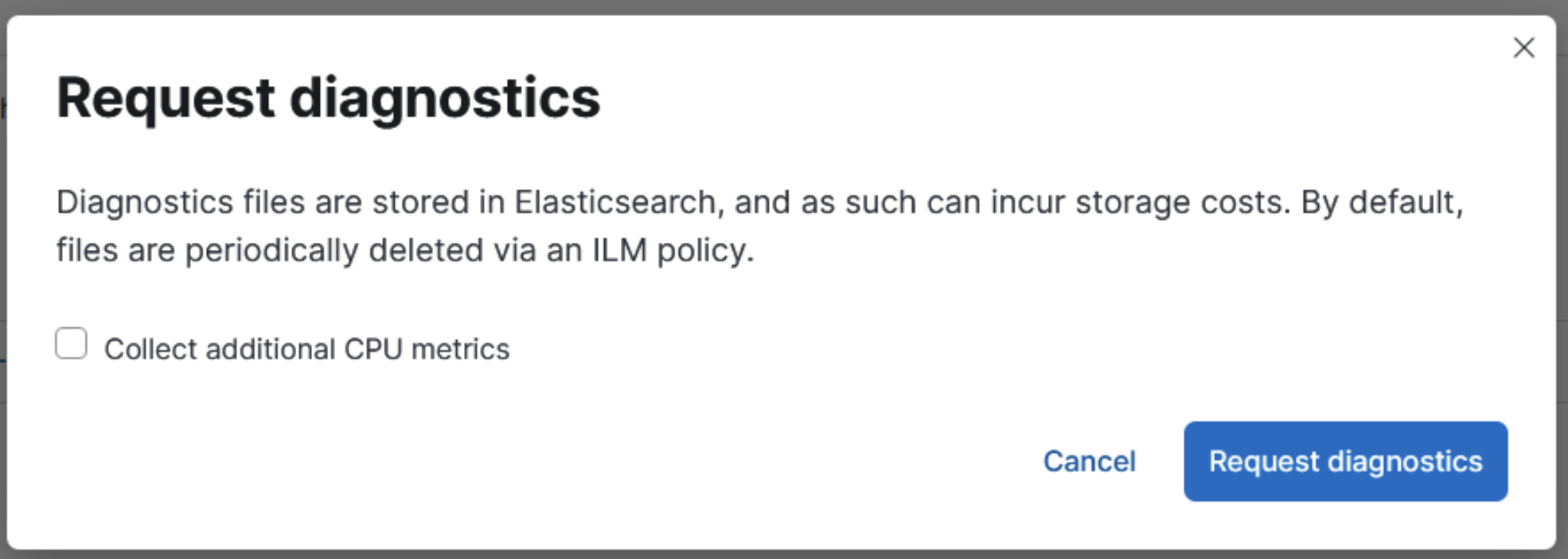
Click the Request diagnostics button.
When it is available, the new diagnostics bundle is listed on the Diagnostics tab along with any in-progress or previously collected bundles for the Elastic Agent.
The diagnostics bundles are stored in Elasticsearch and are removed automatically after 7 days. You can also delete any previously created bundles by clicking the trash can icon.
Run the diagnostics command in the Elastic Agent's install directory. Depending on your operating system, run:
Linux-based systems
cd /opt/Elastic/Agent .elastic-agent diagnosticsWindows Powershell
cd "C:\Program Files\Elastic\Agent" .\elastic-agent.exe diagnosticsApple MacOS
sudo -i cd /Library/Elastic/Agent ./elastic-agent diagnosticsDocker
- Determine the container ID with Docker
ps.
docker ps | grep "beats/elastic-agent"- Use Docker
execto run the diagnostics, replacing theCONTAINER_IDplaceholder.
docker exec -it CONTAINER_ID elastic-agent diagnosticsNote the filename and location of the output file.
- Use Docker
cpto copy the diagnostic file to your local machine, replacing theCONTAINER_IDandFILE_NAMEplaceholders:
docker cp CONTAINER_ID:/usr/share/elastic-agent/FILE_NAME FILE_NAME- Determine the container ID with Docker
Kubernetes
- Determine the container ID with
get.
kubectl get pods --all-namespaces | grep agent- Run the diagnostics with
exec, replacing theNAMESPACEandPOD_NAMEplaceholders:
kubectl exec --stdin --tty POD_NAME -n NAMESPACE -- elastic-agent diagnosticsNote the filename and location of the output file.
- Use
cpto copy the diagnostic file to your local machine, replacing theNAMESPACE,POD_NAME, andFILE_NAMEplaceholders.
kubectl cp NAMESPACE/POD_NAME:FILE_NAME FILE_NAME- Determine the container ID with
Elastic Agent attempts to automatically redact credentials and API keys when creating its diagnostic files. Review the contents of the archive before sharing it to ensure that all forms of organizational private information is censored as needed. For example, ensure:
There are no credentials in plain text in the
*.yamldiagnostic files.The raw form of events failing to output is shown in
*.ndjson. By default, onlywarnlogs are registered. To log all events, enable thedebuglogging level. If you want to omit the raw events from the diagnostics, add the flag--exclude-events.