AI-powered SIEM migration
This feature is in technical preview. It may change in the future, and you should exercise caution when using it in production environments. Elastic will work to fix any issues, but features in technical preview are not subject to the support SLA of GA features.
Elastic's AI-powered SIEM migration helps you quickly convert SIEM rules from the Splunk Processing Language (SPL) to the Elasticsearch Query Language (ES|QL). It simplifies onboarding by matching your rules to Elastic-authored rules, if comparable rules exist. Otherwise, it automatically translates rules on the fly so you can verify and edit them instead of rewriting them from scratch.
You can ingest your data before migrating your rules, or migrate your rules first, in which case the tool will recommend which data sources you need to power your migrated rules.
- A working LLM connector.
- Elastic Stack users: an Enterprise subscription.
- {{Stack users}}: machine learning must be enabled.
- Serverless users: a Security Complete subscription.
Find Get started in the navigation menu or use the global search bar.
Under Configure AI provider select a model, or add a new one. For information on how different models perform, refer to the LLM performance matrix.
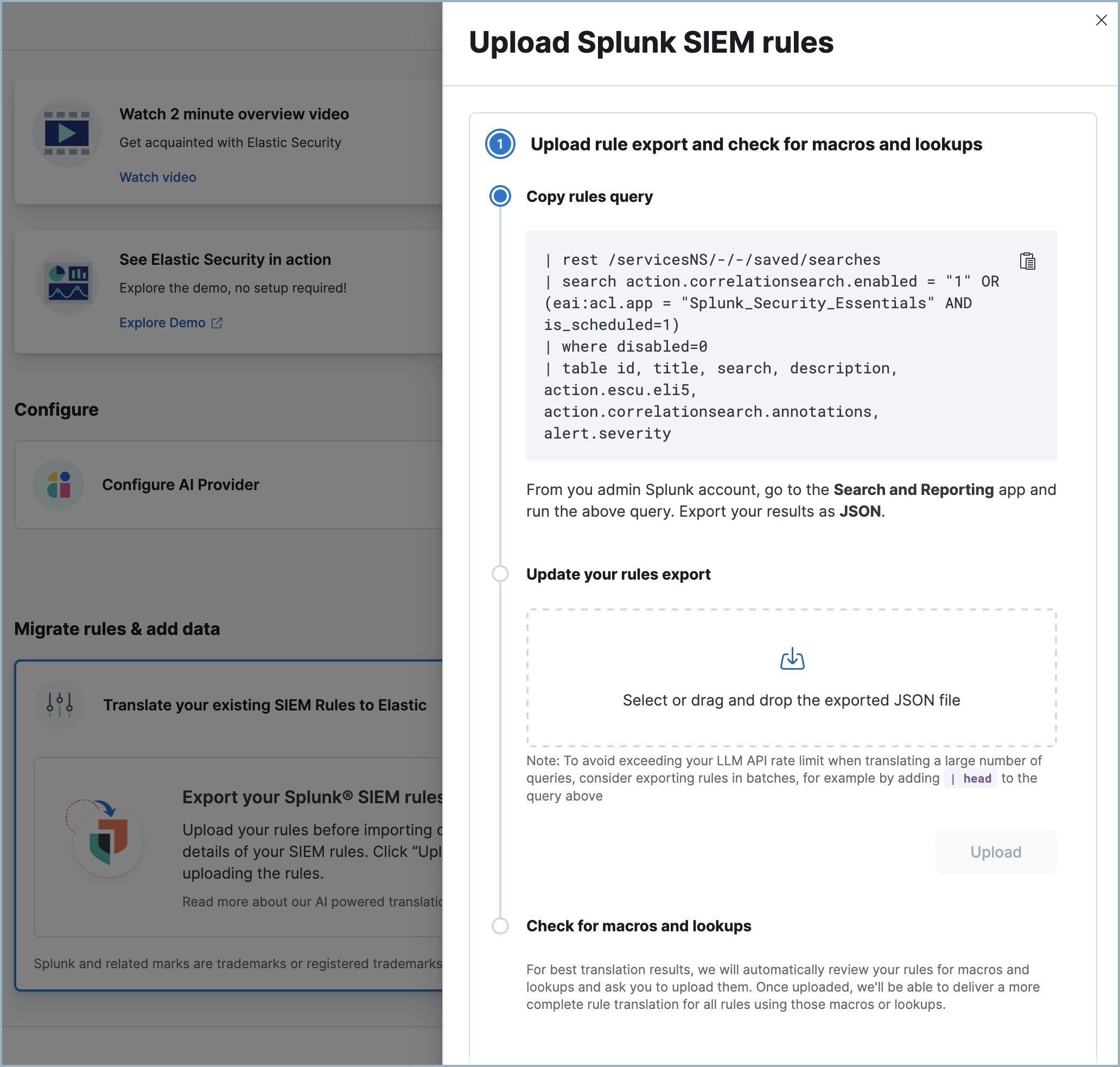
Next, under Migrate rules & add data, click Translate your existing SIEM rules to Elastic, then Upload rules.
Follow the instructions on the Upload Splunk SIEM rules flyout to export your rules from Splunk as JSON.
 Note
NoteThe provided query downloads Splunk correlation rules and saved searches. Alternatively, as long as you export your results in a JSON format, you can use a different query. For example:
| rest /servicesNS/-/-/saved/searches | search is_scheduled=1 AND eai:acl.app=splunksysmonsecurity | where disabled=0 | table id, title, search, description, action.escu.eli5,Which would download rules related to just the
splunksysmonsecurityapp.We don't recommend downloading all searches (for example with
| rest /servicesNS/-/-/saved/searches) since most of the data will be irrelevant to SIEM rule migration.Select your JSON file and click Upload.
NoteIf the file is large, you may need to separate it into multiple parts and upload them individually to avoid exceeding your LLM's context window.
After you upload your Splunk rules, SIEM migration will detect whether they use any Splunk macros or lookups. If so, follow the instructions which appear to export and upload them. Alternatively, you can complete this step later — however, until you upload them, some of your migrated rules will have a
partially translatedstatus.Click Translate to start the rule translation process. You don't need to stay on this page. A notification will appear when the process is complete.
When migration is complete, click the notification or return to the Get started page then click View translated rules to open the Translated rules page.
This section describes the Translated rules page's interface and explains how the data that appears here is derived.
When you upload a new batch of rules, they are assigned a name and number, for example SIEM rule migration 1, or SIEM rule migration 2. Use the Migrations dropdown menu in the upper right to select which batch appears.
The table's fields are as follows:
Name: The names of Elastic authored rules cannot be edited until after rule installation. To edit the name of a custom translated rule, click the name and select Edit.
Status: The rule's translation status. Hover over the tooltip next to the column title for more information.
Risk Score: For Elastic authored rules, risk scores are predefined. For custom translated rules, risk scores are defined as follows:
- If the source rule has a field comparable to Elastic's risk score, we use that value.
- Otherwise, if the source rule has a field comparable to Elastic's rule severity field, we base the risk score on that value according to these guidelines.
- Otherwise, a default value is assigned.
Rule severity: For Elastic authored rules, severity scores are predefined. For custom translated rules, risk scores are based on the source rule's severity field. Splunk severity scores are translated to Elastic rule severity scores as follows:
Splunk severity Elastic rule severity (Info) Low (Low) Low (Medium) Medium (High) High (Critical) Critical Author: Shows one of two possible values:
Elastic, orCustom. Elastic authored rules are created by Elastic and update automatically. Custom rules are translated by the SIEM migration tool or your team, and do not update automatically.Integrations: Shows the number of Elastic integrations that must be installed to provide data for the rule to run successfully.
Actions: Allows you to click Install to add a rule to Elastic. Installed rules must also be enabled before they will run. To install rules in bulk, select the check box at the top of the table before clicking Install.
Once you're on the Translated rules page, to install any rules that were partially translated or not translated, you will need to edit them. Optionally, you can also edit custom rules that were successfully translated to finetune them.
You cannot edit Elastic authored rules using this interface, but after they are installed you can edit them from the Rules page.
Click the rule's name to open the rule's details flyout to the Translation tab, which shows the source rule alongside the translated — or partially translated — Elastic version. You can update any part of the rule. When finished, click Save.
If you haven't yet ingested your data, you will likely encounter Unknown index or Unknown column errors while editing. You can ignore these and add your data later.
The rule details flyout which appears when you click on a rule's name in the Translate rules table has two other tabs, Overview and Summary. The Overview tab displays information such as the rule's severity, risk score, rule type, and how frequently it runs. The Summary tab explains the logic behind how the rule was translated, such as why specific ES|QL commands were used, or why a source rule was mapped to a particular Elastic authored rule.