Trusted devices
By default, Elastic Defend policies have device control enabled, with access level set to block all operations. This prevents external storage devices from connecting to protected hosts.
- Device control only affects external USB storage devices. It does not affect other peripherals such as Yubikeys, webcams, or keyboards.
- Device control only supports Windows and Mac endpoints.
Trusted devices are specific external devices that are allowed to connect to your protected hosts regardless of device control settings. Create trusted devices to avoid interfering with expected workflows that involve known hardware.
By default, a trusted device is recognized globally across all hosts running Elastic Defend. You can also assign a trusted device to a specific Elastic Defend integration policy, enabling the device to be trusted by only the hosts assigned to that policy.
Add a trusted device to exempt it from device control:
Depending on your version, do one of the following:
-
Go to the Artifacts page using the navigation menu or the global search field, then select the Trusted devices tab. -
Go to the Trusted Devices page using the navigation menu or the global search field.
-
Click + Add trusted device. The Add trusted device flyout opens.
Name your trusted device and give it a description.
In the Conditions section, specify the operating system(s) and the
Device ID.Select an option in the Assignment section:
- Global: Assign the trusted device to all Elastic Defend integration policies.
- Per Policy: Assign the trusted device to one or more specific Elastic Defend integration policies.
Click Add trusted device.
To add multiple trusted devices at once, you can import an NDJSON file instead. Refer to Import and export trusted devices.
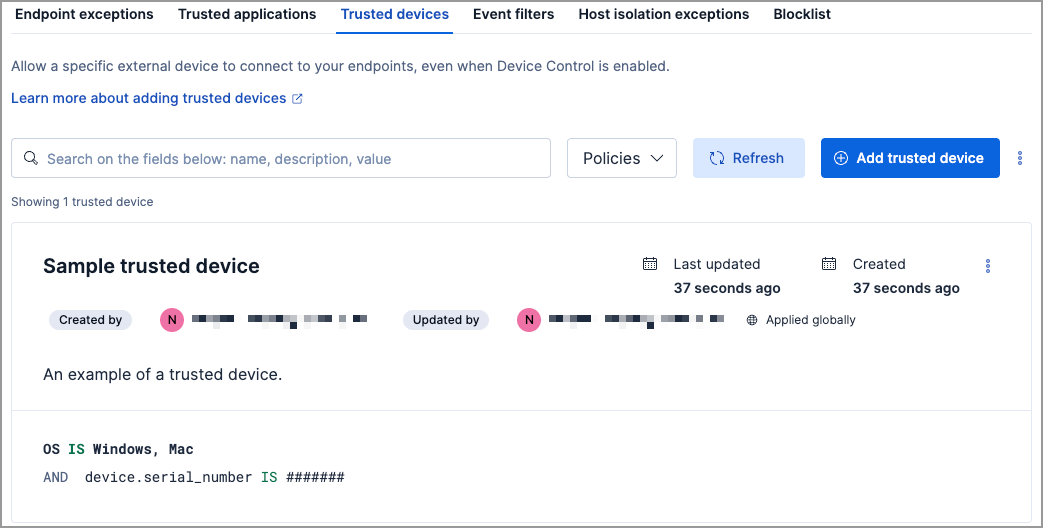
The Trusted devices UI displays all the trusted devices that have been added to the Elastic Security app. To refine the list, use the search bar to search by name, description, or field value.
- To export trusted devices, you need the Trusted Devices: Read privilege.
- To import per-policy items, you need the Trusted Devices: All privilege.
- To import global items, you need the Trusted Devices: All and the Global artifact management: All privilege.
- To import items to a different space, you need the Global artifact management: All privilege.
You can import and export trusted devices as NDJSON files:
- When the list is empty: click Import trusted devices.
- When the list has entries: click the actions menu ( ), then select Import trusted devices or Export trusted devices.
When you import an NDJSON file, the imported trusted devices are appended to your existing entries — existing entries are not removed or overwritten.
Items are processed individually on import — per-policy items that are not visible in the current space are skipped, while the remaining items are imported.
If an imported per-policy item is assigned to a policy that doesn't exist in the current environment, the item is imported with the policy assignment removed.
You can individually modify each trusted device. You can also change the policies that a trusted device is assigned to.
To edit a trusted device:
- Click the actions menu (…) on the trusted device you want to edit, then select Edit trusted device.
- Modify details as needed.
- Click Save.
You can delete a trusted device, which removes it entirely from all Elastic Defend integration policies.
To delete a trusted device:
- Click the actions menu (…) on the trusted device you want to delete, then select Delete trusted device.
- On the dialog that opens, verify that you are removing the correct device, then click Delete. A confirmation message appears.